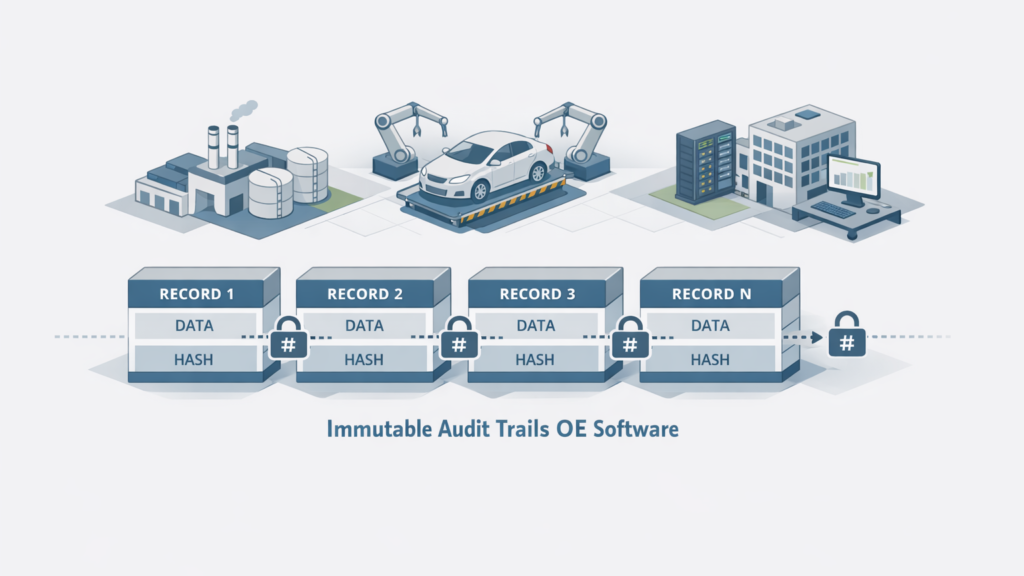
This article explains how to design and implement compliance‑ready immutable audit trails for Original Equipment (OE) software. It is written for IT leaders, architects, compliance officers and engineering teams in the mid‑market, industrial and manufacturing sectors, enterprise environments and the automotive industry. The goal is a practical, actionable blueprint you can adapt to your stack.
Why immutable audit trails matter for OE software
OE software controls product configuration, firmware updates, production processes and traceability data. Immutable audit trails provide a tamper‑resistant record of who did what, when, and in what context. They support regulatory compliance (e.g., ISO, FDA, automotive standards), incident investigation, warranty and liability cases, and supply‑chain transparency.

Regulatory and industry requirements to consider
- Automotive: requirements around functional safety, software traceability and secure update logs.
- Manufacturing & enterprise: quality management standards (ISO 9001), supplier traceability and change control records.
- Data protection and retention: alignment with local regulations for personal data and retention periods.
- Auditability: ability to produce reliable records for internal and external audits, including cryptographic verification where required.
Core technical properties of a compliance‑ready immutable audit trail
- Write‑once, append‑only storage: records cannot be modified or deleted without detection.
- Cryptographic integrity: hashes, signatures or MACs to guarantee tamper evidence and chain integrity.
- Provenance metadata: actor identity, timestamps, source system, request context, and relevant object state.
- Non‑repudiation: mechanisms to link actions to authenticated principals (keys, certificates, or strong identity providers).
- Availability and durability: storage and replication strategy that meets retention and recovery SLAs.
- Searchable and exportable: structured indexes and standard export formats for audits and eDiscovery.
Design patterns and data models
Design audit events as structured, versioned records. Key fields include event_id, timestamp (UTC, monotonic where required), actor_id, actor_role, action_type, target_resource, pre_state_hash, post_state_hash, and context. Keep the payload minimal and reference larger artifacts off‑chain or by content hash to avoid bloating the trail.
Implementation options and tradeoffs
- Immutable storage layers: WORM (write once read many) object stores or append‑only databases. Pros: simple, proven. Cons: can be expensive for high write volumes.
- Cryptographic chaining: each record includes hash of prior record. Pros: strong tamper evidence. Cons: requires careful handling for sharded or distributed systems.
- Ledger technologies: permissioned ledger or blockchain for multi‑party trust scenarios. Pros: decentralized trust and auditability. Cons: complexity, integration cost, and performance considerations.
- Hybrid approaches: store proofs (hashes, signatures) in an immutable anchor (external ledger or notarization service) while keeping full records in optimized storage.
Operational controls, retention and eDiscovery
Define retention policies aligned to regulatory and business requirements. Implement role‑based access for viewing and exporting audit data; restrict write capabilities strongly. Provide reliable export and search tools for audits and legal discovery, including cryptographic verification steps documented in procedures.
Integration with existing OE systems and supply chains
Integrate audit generation at the system boundary: CI/CD pipelines, device update services, MES/ERP events, and supplier portals. Standardize event schemas across teams and suppliers. Use message queues and event brokers to decouple producers and the audit ingestion pipeline, ensuring no loss under load.
Verification, monitoring and audit processes
- Automate integrity checks: periodic verification of hashes, signature validation and end‑to‑end reconciliation.
- Alerting: detect anomalous patterns (mass deletions attempts, out‑of‑window timestamps, or actor anomalies).
- Audit playbooks: documented steps for auditors to verify trail integrity and reproduce verification artifacts.
Common pitfalls and mitigation
- Mixing logs and audit trails: logs are transient; audit trails must be controlled and tamper‑resistant. Separate concerns and storage.
- Poor identity binding: weak authentication undermines non‑repudiation. Use strong identity and key management.
- Ignoring scale: design for expected ingest volumes and retention growth to avoid performance degradation.
- Overreliance on a single verifier: combine cryptographic proofs with operational controls and third‑party attestation where needed.
Next steps for teams
Start with a requirements inventory mapping regulations, retention needs and key systems. Prototype an append‑only trail using your existing object store plus cryptographic chaining or anchoring. Validate with a sample audit and a dry‑run with auditors. Scale iteratively and include suppliers and downstream systems once the core trail is verified.
Services: involve security architecture, compliance, and platform engineering early. Use established procedures (CTA‑Rules) for change control, key management and auditor access. Keep documentation current and accessible to internal and external auditors.
FAQ
What makes an audit trail truly immutable?
An immutable audit trail uses append‑only storage combined with cryptographic integrity (hashes or signatures) and strict write controls so records cannot be altered or deleted without detection.
Do I need blockchain for a compliance‑ready trail?
Not necessarily. Permissioned ledgers can help in multi‑party trust scenarios, but many organizations achieve compliance with append‑only object stores, cryptographic chaining and off‑chain anchoring.
How long should audit records be retained?
Retention depends on regulatory, contractual and business needs. Map applicable regulations and legal requirements, then codify retention and deletion procedures aligned with those mandates.
How do I prove integrity to an external auditor?
Provide the trail exports, the verification scripts or procedures, cryptographic proofs (hashes, signatures), and documentation of key management and access controls so auditors can reproduce integrity checks.
Ready to make your OE software audit‑ready? Assemble a cross‑functional pilot team—security, compliance and platform engineering—to map requirements and build a minimal proof of concept. Document CTA‑Rules for key management and auditor access as part of the pilot.